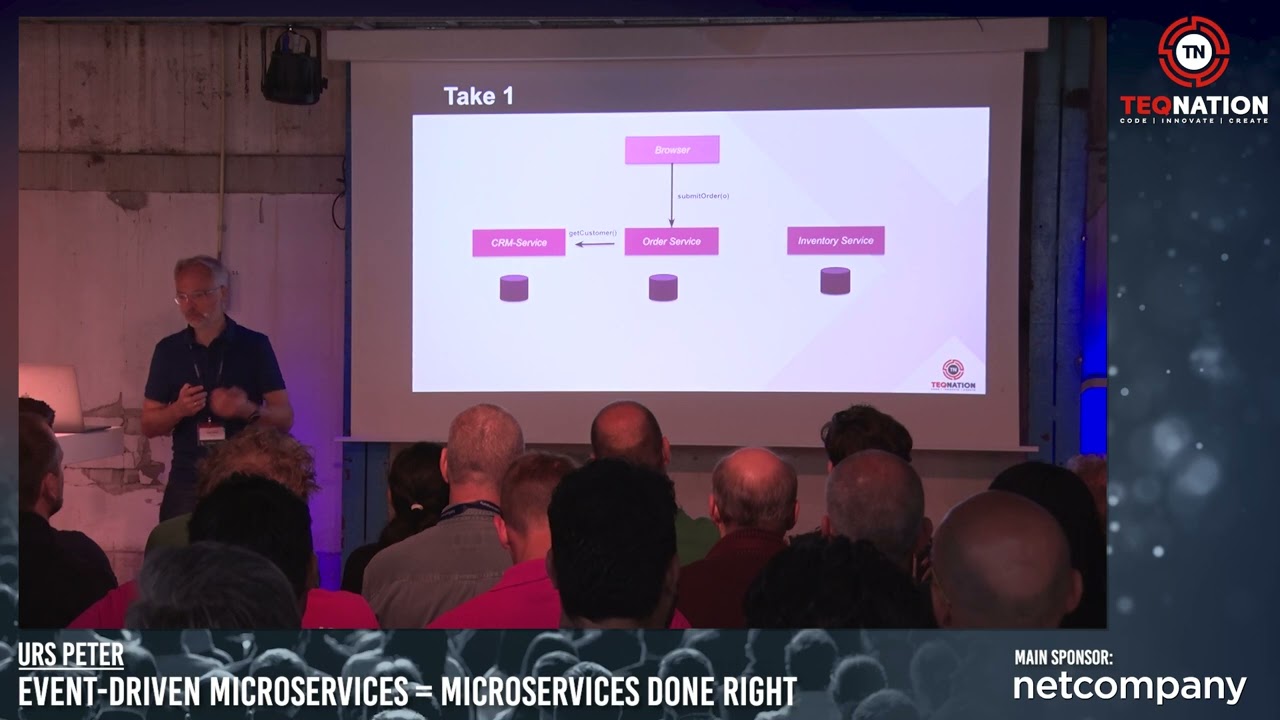
Join us on May 22nd at DeFabrique in Utrecht, Netherlands, for an unforgettable experience where developers, architects, and tech enthusiasts come together to explore the future of technology. Countdown untill the TEQnation Conference: Don’t miss out – mark your calendars for May 22nd and secure your spot at TEQnation 2024!
Session Highlights
At TEQnation, you can expect sessions covering a diverse range of topics including Artificial Intelligence & Machine Learning, IoT & Embedded Systems, Modern Infrastructure, Security, and more. Dive deep into the latest trends, gain practical knowledge, and connect with industry experts.
Take a look at some of the exciting sessions lined up for TEQnation 2024. Get ready to code, innovate, and create with fellow developers!

Erik Meijer
Senior Director of Engineering @ Facebook
Automind: Enterprise-Grade AI Assistants Done Right
Join us for a captivating keynote session with Erik Meijer, and discover how our Automind platform tackles the complexities of deploying AI agents in enterprise environments while prioritizing security, reliability, and scalability. Learn how we integrate classic computer science with modern large language models to create robust, intelligent assistants that are tailored to meet enterprise requirements. Don’t miss out on this insightful talk that explores the key insights behind Automind and how we overcame formidable technical challenges to deliver unparalleled AI solutions.
Time: 09:40 – 10:05
Track: Artificial Intelligence & Machine Learning

Deepu K Sasidharan
Staff Developer Advocate @ Okta
Time: 11:00 – 11:45
Track: Security
A Passwordless Future! Passkeys for Developers
Weak passwords remain a significant concern for security, but the Web Authentication standard offers a solution through passkeys. Discover how passkeys, the latest in authentication technology used by platforms like Google and GitHub, leverage public key cryptography and biometrics/hardware authenticators to enhance security and usability. In this session, we’ll delve into the architecture of passkeys, their pros and cons, and how developers can implement them using WebAuthn libraries. Don’t miss the demos demonstrating the integration of passkeys into web applications!
How to write maintainable code in a large organisation
Join this session where Ragna addresses the challenges of code duplication within large organizations and shares strategies for removing duplication and promoting efficient collaboration. Using examples from a Java-based Spring Boot application in a microservices architecture, she demonstrates best practices and potential pitfalls. By the end of the presentation, attendees will gain insights into simplifying development processes and reducing code duplication, ultimately fostering happier developers.

Ragna Gerretsen
Software Engineer @ Rabobank
Time: 12:00 – 12:45
Track: Modern Infrastructure